印度的一个比赛,花了一整天,只做出一道逆向。几天过去了,终于决定把题解写一下。
本次比赛的所有二进制题目可以到http://file.iyzyi.com/?dir=CTF/hackim20 下载。
好了,言归正传。看一下这道题目。
给出了三个文件,
blob,二进制文件,不是程序,main,二进制程序deploy.py,从blob读取数据,然后调用main
main
先来看一下main:
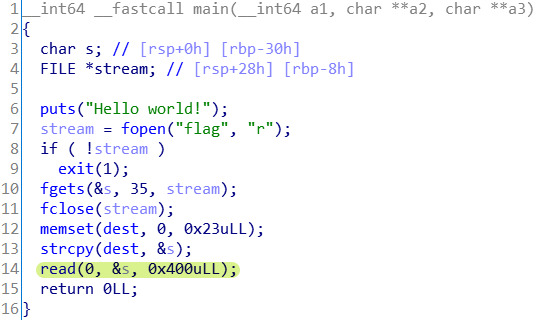
从文件读入flag,然后放入dest处(0x4040a0)
明显的栈缓冲区溢出。
blob
然后是blob:
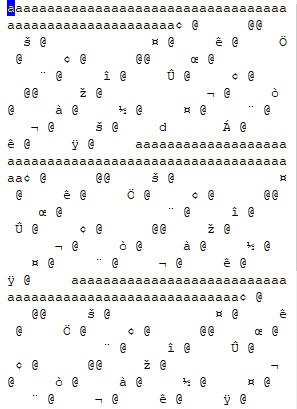
a的字符数量正好是main中可以利用栈缓冲区溢出漏洞的数量。
deploy.py
最后是deploy.py:
import subprocess
# 每条payload在`blob`中的长度
o = [296, 272, 272, 272, 296, 360, 272, 424, 272, 208, 120, 120, 120, 96, 120, 120, 120, 120, 120, 120, 120, 208, 120, 120, 208, 208, 208, 208, 208, 272, 120, 208, 208]
# flag的密文
r = [208, 225, 237, 20, 214, 183, 79, 105, 207, 217, 125, 66, 123, 104, 97, 99, 107 , 105, 109, 50, 48, 202, 111, 111, 29, 63, 223, 36, 0, 124, 100, 219, 32]
cmd = ['./main']
rets = []
with open('blob', 'rb') as f:
for offset in o:
# 从blob中读取payload
# 读完一个payload,文件读取的光标就会下移到下一条payload的开始的地方
data = f.read(offset)
# 调用main
p = subprocess.Popen(cmd, stdin=subprocess.PIPE)
# 向main传入payload
p.stdin.write(data)
# 等待main把结果返回
p.communicate()
# 每次运行得到密文的一位(main的返回值就是flag密文中的一位)
rets.append(p.returncode)
# 判断密文是否相等
if all([rets[i] == r[i] for i in range(len(r))]):
print('Yes!')
else:
print('No!')payload
关键在于提取blob中的payload。
下面的程序获取payload中的跳转地址:
o = [296, 272, 272, 272, 296, 360, 272, 424, 272, 208, 120, 120, 120, 96, 120, 120, 120, 120, 120, 120, 120, 208, 120, 120, 208, 208, 208, 208, 208, 272, 120, 208, 208]
with open('blob', 'rb') as f:
line_list = []
for offset in o:
data = f.read(offset)[56:]
for i in range(len(data)//8):
hex_data = "".join("{:02x}".format(c) for c in data[8*i:8*i+8][::-1])
line_list.append(hex_data)
for i in line_list:
print(i)很长,所以这里不全列出,只放出前几个跳转地址:
00000000004011a2
00000000004040a0
000000000040119a
0000000000000000
00000000004011a4ROP
ida打开main,来到相关地址处:
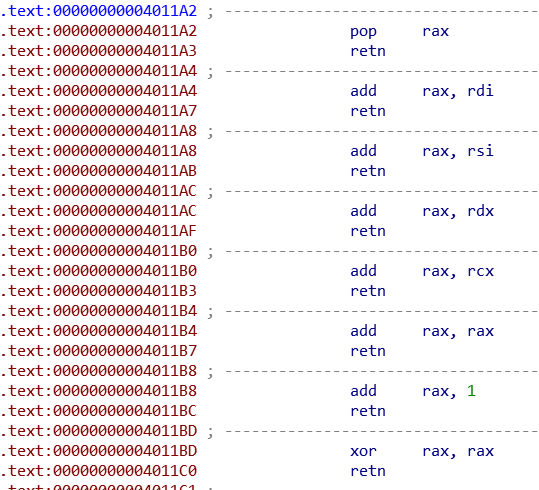
很明显的ROP.
将此处的相关的所有代码复制保存到code.txt中:
.text:0000000000401196 sub_401196 proc near
.text:0000000000401196 ; __unwind {
.text:0000000000401196 push rbp
.text:0000000000401197 mov rbp, rsp
.text:000000000040119A pop rdi
.text:000000000040119B retn
.text:000000000040119B sub_401196 endp
.text:000000000040119B
.text:000000000040119C ; ---------------------------------------------------------------------------
.text:000000000040119C pop rsi
.text:000000000040119D retn
.text:000000000040119E ; ---------------------------------------------------------------------------
.text:000000000040119E pop rdx
.text:000000000040119F retn
.text:00000000004011A0 ; ---------------------------------------------------------------------------
.text:00000000004011A0 pop rcx
.text:00000000004011A1 retn
.text:00000000004011A2 ; ---------------------------------------------------------------------------
.text:00000000004011A2 pop rax
.text:00000000004011A3 retn
.text:00000000004011A4 ; ---------------------------------------------------------------------------
.text:00000000004011A4 add rax, rdi
.text:00000000004011A7 retn
.text:00000000004011A8 ; ---------------------------------------------------------------------------
.text:00000000004011A8 add rax, rsi
.text:00000000004011AB retn
.text:00000000004011AC ; ---------------------------------------------------------------------------
.text:00000000004011AC add rax, rdx
.text:00000000004011AF retn
.text:00000000004011B0 ; ---------------------------------------------------------------------------
.text:00000000004011B0 add rax, rcx
.text:00000000004011B3 retn
.text:00000000004011B4 ; ---------------------------------------------------------------------------
.text:00000000004011B4 add rax, rax
.text:00000000004011B7 retn
.text:00000000004011B8 ; ---------------------------------------------------------------------------
.text:00000000004011B8 add rax, 1
.text:00000000004011BC retn
.text:00000000004011BD ; ---------------------------------------------------------------------------
.text:00000000004011BD xor rax, rax
.text:00000000004011C0 retn
.text:00000000004011C1 ; ---------------------------------------------------------------------------
.text:00000000004011C1 sub rax, rdi
.text:00000000004011C4 retn
.text:00000000004011C5 ; ---------------------------------------------------------------------------
.text:00000000004011C5 sub rax, rsi
.text:00000000004011C8 retn
.text:00000000004011C9 ; ---------------------------------------------------------------------------
.text:00000000004011C9 sub rax, rdx
.text:00000000004011CC retn
.text:00000000004011CD ; ---------------------------------------------------------------------------
.text:00000000004011CD sub rax, rcx
.text:00000000004011D0 retn
.text:00000000004011D1 ; ---------------------------------------------------------------------------
.text:00000000004011D1 sub rax, 1
.text:00000000004011D5 retn
.text:00000000004011D6 ; ---------------------------------------------------------------------------
.text:00000000004011D6 movzx rdi, byte ptr [rdi]
.text:00000000004011DA retn
.text:00000000004011DB ; ---------------------------------------------------------------------------
.text:00000000004011DB movzx rsi, byte ptr [rsi]
.text:00000000004011DF retn
.text:00000000004011E0 ; ---------------------------------------------------------------------------
.text:00000000004011E0 movzx rdx, byte ptr [rdx]
.text:00000000004011E4 retn
.text:00000000004011E5 ; ---------------------------------------------------------------------------
.text:00000000004011E5 movzx rcx, byte ptr [rcx]
.text:00000000004011E9 retn
.text:00000000004011EA ; ---------------------------------------------------------------------------
.text:00000000004011EA mov rdi, rax
.text:00000000004011ED retn
.text:00000000004011EE ; ---------------------------------------------------------------------------
.text:00000000004011EE mov rsi, rax
.text:00000000004011F1 retn
.text:00000000004011F2 ; ---------------------------------------------------------------------------
.text:00000000004011F2 mov rdx, rax
.text:00000000004011F5 retn
.text:00000000004011F6 ; ---------------------------------------------------------------------------
.text:00000000004011F6 mov rcx, rax
.text:00000000004011F9 retn
.text:00000000004011FA ; ---------------------------------------------------------------------------
.text:00000000004011FA mov edi, 0
.text:00000000004011FF call _exit
.text:00000000004011FF ; } // starts at 401196然后通过下面的脚本将提取出上面代码的行号和汇编指令,生成一个字典:
import re
with open(r'code.txt','r',encoding='utf-8') as f:
code = f.read()
code = re.sub(r'\.text.+?;.+?\n', '', code)
code = '\n'.join(code.split('\n')[1:])
code_iter = re.finditer(r'\.text\:(.{16}) +?(.+?)\n',code)
code_dist = {}
for i in code_iter:
code_dist[i.group(1)] = i.group(2).lstrip()
print(code_dist)生成汇编代码
接下来就很简单了,把行号和汇编对应,将payload执行的语句罗列出来,下面的脚本是总脚本,包括上面的两个子程序:
import re
o = [296, 272, 272, 272, 296, 360, 272, 424, 272, 208, 120, 120, 120, 96, 120, 120, 120, 120, 120, 120, 120, 208, 120, 120, 208, 208, 208, 208, 208, 272, 120, 208, 208]
with open('blob', 'rb') as f:
line_list = []
for offset in o:
# 不读取字符a
data = f.read(offset)[56:]
for i in range(len(data)//8):
hex_data = "".join("{:02x}".format(c) for c in data[8*i:8*i+8][::-1])
line_list.append(hex_data)
with open(r'code.txt','r',encoding='utf-8') as f:
code = f.read()
code = re.sub(r'\.text.+?;.+?\n', '', code)
code = '\n'.join(code.split('\n')[1:])
code_iter = re.finditer(r'\.text\:(.{16}) +?(.+?)\n',code)
code_dist = {}
for i in code_iter:
code_dist[i.group(1)] = i.group(2).lstrip()
print(code_dist)
asm_code = ''
for i in range(len(line_list)):
if line_list[i].upper() in code_dist.keys():
line_list[i] = line_list[i] + ' %s' % code_dist[line_list[i].upper()]
else:
if re.search(r'00000000000000', line_list[i]):
line_list[i] = line_list[i] + ' %d' % int(line_list[i],16)
asm_code += line_list[i] + '\n'
print(asm_code)
with open(r'asm_code.txt','w') as f:
f.write(asm_code)输出所有payload执行的命令,我做了一些注释:
每一个payload都是一大段代码,每一大段代码的后面都紧跟着两行注释,第一个是一个数字,表示这是第几个payload;第二行的注释表示变量之间的操作,比如第一个payload的;0+2+4 -100是指第0个变量+第二个变量+第四个变量减去100等于第一个payload的密文数据(即deploy.py中的r[0],208)
00000000004011a2 pop rax
00000000004040a0
000000000040119a pop rdi
0000000000000000 0
00000000004011a4 add rax, rdi
00000000004011ea mov rdi, rax
00000000004011d6 movzx rdi, byte ptr [rdi]
00000000004011a2 pop rax
00000000004040a0
000000000040119c pop rsi
0000000000000002 2
00000000004011a8 add rax, rsi
00000000004011ee mov rsi, rax
00000000004011db movzx rsi, byte ptr [rsi]
00000000004011a2 pop rax
00000000004040a0
000000000040119e pop rdx
0000000000000004 4
00000000004011ac add rax, rdx
00000000004011f2 mov rdx, rax
00000000004011e0 movzx rdx, byte ptr [rdx]
00000000004011bd xor rax, rax
00000000004011a4 add rax, rdi
00000000004011a8 add rax, rsi
00000000004011ac add rax, rdx
000000000040119a pop rdi
0000000000000064 100
00000000004011c1 sub rax, rdi
00000000004011ea mov rdi, rax
00000000004011ff call _exit
;1
;0+2+4 -100
00000000004011a2 pop rax
00000000004040a0
000000000040119a pop rdi
0000000000000006 6
00000000004011a4 add rax, rdi
00000000004011ea mov rdi, rax
00000000004011d6 movzx rdi, byte ptr [rdi]
00000000004011a2 pop rax
00000000004040a0
000000000040119c pop rsi
0000000000000008 8
00000000004011a8 add rax, rsi
00000000004011ee mov rsi, rax
00000000004011db movzx rsi, byte ptr [rsi]
00000000004011a2 pop rax
00000000004040a0
000000000040119e pop rdx
000000000000000a 10
00000000004011ac add rax, rdx
00000000004011f2 mov rdx, rax
00000000004011e0 movzx rdx, byte ptr [rdx]
00000000004011bd xor rax, rax
00000000004011a4 add rax, rdi
00000000004011a8 add rax, rsi
00000000004011ac add rax, rdx
00000000004011ea mov rdi, rax
00000000004011ff call _exit
;2
;6+8+10
00000000004011a2 pop rax
00000000004040a0
000000000040119a pop rdi
000000000000000c 12
00000000004011a4 add rax, rdi
00000000004011ea mov rdi, rax
00000000004011d6 movzx rdi, byte ptr [rdi]
00000000004011a2 pop rax
00000000004040a0
000000000040119c pop rsi
000000000000000e 14
00000000004011a8 add rax, rsi
00000000004011ee mov rsi, rax
00000000004011db movzx rsi, byte ptr [rsi]
00000000004011a2 pop rax
00000000004040a0
000000000040119e pop rdx
0000000000000010 16
00000000004011ac add rax, rdx
00000000004011f2 mov rdx, rax
00000000004011e0 movzx rdx, byte ptr [rdx]
00000000004011bd xor rax, rax
00000000004011a4 add rax, rdi
00000000004011a8 add rax, rsi
00000000004011ac add rax, rdx
00000000004011ea mov rdi, rax
00000000004011ff call _exit
;3
;12+14+16
00000000004011a2 pop rax
00000000004040a0
000000000040119a pop rdi
0000000000000012 18
00000000004011a4 add rax, rdi
00000000004011ea mov rdi, rax
00000000004011d6 movzx rdi, byte ptr [rdi]
00000000004011a2 pop rax
00000000004040a0
000000000040119c pop rsi
0000000000000001 1
00000000004011a8 add rax, rsi
00000000004011ee mov rsi, rax
00000000004011db movzx rsi, byte ptr [rsi]
00000000004011a2 pop rax
00000000004040a0
000000000040119e pop rdx
000000000000001e 30
00000000004011ac add rax, rdx
00000000004011f2 mov rdx, rax
00000000004011e0 movzx rdx, byte ptr [rdx]
00000000004011bd xor rax, rax
00000000004011a4 add rax, rdi
00000000004011a8 add rax, rsi
00000000004011c9 sub rax, rdx
00000000004011ea mov rdi, rax
00000000004011ff call _exit
;4
;18+1-30
00000000004011a2 pop rax
00000000004040a0
000000000040119a pop rdi
0000000000000003 3
00000000004011a4 add rax, rdi
00000000004011ea mov rdi, rax
00000000004011d6 movzx rdi, byte ptr [rdi]
00000000004011a2 pop rax
00000000004040a0
000000000040119c pop rsi
0000000000000016 22
00000000004011a8 add rax, rsi
00000000004011ee mov rsi, rax
00000000004011db movzx rsi, byte ptr [rsi]
00000000004011a2 pop rax
00000000004040a0
000000000040119e pop rdx
0000000000000003 3
00000000004011ac add rax, rdx
00000000004011f2 mov rdx, rax
00000000004011e0 movzx rdx, byte ptr [rdx]
00000000004011bd xor rax, rax
00000000004011a4 add rax, rdi
00000000004011a8 add rax, rsi
00000000004011ac add rax, rdx
000000000040119a pop rdi
0000000000000064 100
00000000004011c1 sub rax, rdi
00000000004011ea mov rdi, rax
00000000004011ff call _exit
;5
;3+22+3 -100
00000000004011a2 pop rax
00000000004040a0
000000000040119a pop rdi
0000000000000005 5
00000000004011a4 add rax, rdi
00000000004011ea mov rdi, rax
00000000004011d6 movzx rdi, byte ptr [rdi]
00000000004011a2 pop rax
00000000004040a0
000000000040119c pop rsi
000000000000001d 29
00000000004011a8 add rax, rsi
00000000004011ee mov rsi, rax
00000000004011db movzx rsi, byte ptr [rsi]
00000000004011a2 pop rax
00000000004040a0
000000000040119e pop rdx
000000000000001c 28
00000000004011ac add rax, rdx
00000000004011f2 mov rdx, rax
00000000004011e0 movzx rdx, byte ptr [rdx]
00000000004011a2 pop rax
00000000004040a0
00000000004011a0 pop rcx
0000000000000007 7
00000000004011b0 add rax, rcx
00000000004011f6 mov rcx, rax
00000000004011e5 movzx rcx, byte ptr [rcx]
00000000004011bd xor rax, rax
00000000004011a4 add rax, rdi
00000000004011a8 add rax, rsi
00000000004011ac add rax, rdx
00000000004011cd sub rax, rcx
000000000040119a pop rdi
0000000000000064 100
00000000004011c1 sub rax, rdi
00000000004011ea mov rdi, rax
00000000004011ff call _exit
;6
;5+29+28-7 -100
00000000004011a2 pop rax
00000000004040a0
000000000040119a pop rdi
0000000000000009 9
00000000004011a4 add rax, rdi
00000000004011ea mov rdi, rax
00000000004011d6 movzx rdi, byte ptr [rdi]
00000000004011a2 pop rax
00000000004040a0
000000000040119c pop rsi
0000000000000011 17
00000000004011a8 add rax, rsi
00000000004011ee mov rsi, rax
00000000004011db movzx rsi, byte ptr [rsi]
00000000004011a2 pop rax
00000000004040a0
000000000040119e pop rdx
000000000000000b 11
00000000004011ac add rax, rdx
00000000004011f2 mov rdx, rax
00000000004011e0 movzx rdx, byte ptr [rdx]
00000000004011bd xor rax, rax
00000000004011a4 add rax, rdi
00000000004011a8 add rax, rsi
00000000004011c9 sub rax, rdx
00000000004011ea mov rdi, rax
00000000004011ff call _exit
;7
;9+17-11
00000000004011a2 pop rax
00000000004040a0
000000000040119a pop rdi
0000000000000013 19
00000000004011a4 add rax, rdi
00000000004011ea mov rdi, rax
00000000004011d6 movzx rdi, byte ptr [rdi]
00000000004011a2 pop rax
00000000004040a0
000000000040119c pop rsi
000000000000001b 27
00000000004011a8 add rax, rsi
00000000004011ee mov rsi, rax
00000000004011db movzx rsi, byte ptr [rsi]
00000000004011bd xor rax, rax
00000000004011a4 add rax, rdi
00000000004011a8 add rax, rsi
00000000004011f6 mov rcx, rax ;19+27
00000000004011a2 pop rax
00000000004040a0
000000000040119a pop rdi
000000000000000d 13
00000000004011a4 add rax, rdi
00000000004011ea mov rdi, rax
00000000004011d6 movzx rdi, byte ptr [rdi]
00000000004011a2 pop rax
00000000004040a0
000000000040119c pop rsi
000000000000000f 15
00000000004011a8 add rax, rsi
00000000004011ee mov rsi, rax
00000000004011db movzx rsi, byte ptr [rsi]
00000000004011a2 pop rax
00000000004040a0
000000000040119e pop rdx
0000000000000014 20
00000000004011ac add rax, rdx
00000000004011f2 mov rdx, rax
00000000004011e0 movzx rdx, byte ptr [rdx]
00000000004011bd xor rax, rax
00000000004011a4 add rax, rdi
00000000004011a8 add rax, rsi
00000000004011ac add rax, rdx ;13+15+20
00000000004011cd sub rax, rcx
00000000004011ea mov rdi, rax
00000000004011ff call _exit
;8
;13+15+20-19-27
00000000004011a2 pop rax
00000000004040a0
000000000040119a pop rdi
0000000000000015 21
00000000004011a4 add rax, rdi
00000000004011ea mov rdi, rax
00000000004011d6 movzx rdi, byte ptr [rdi]
00000000004011a2 pop rax
00000000004040a0
000000000040119c pop rsi
0000000000000017 23
00000000004011a8 add rax, rsi
00000000004011ee mov rsi, rax
00000000004011db movzx rsi, byte ptr [rsi]
00000000004011a2 pop rax
00000000004040a0
000000000040119e pop rdx
0000000000000017 23
00000000004011ac add rax, rdx
00000000004011f2 mov rdx, rax
00000000004011e0 movzx rdx, byte ptr [rdx]
00000000004011bd xor rax, rax
00000000004011a4 add rax, rdi
00000000004011a8 add rax, rsi
00000000004011ac add rax, rdx
00000000004011ea mov rdi, rax
00000000004011ff call _exit
;9
;21+23+23
00000000004011a2 pop rax
00000000004040a0
000000000040119a pop rdi
0000000000000019 25
00000000004011a4 add rax, rdi
00000000004011ea mov rdi, rax
00000000004011d6 movzx rdi, byte ptr [rdi]
00000000004011a2 pop rax
00000000004040a0
000000000040119c pop rsi
000000000000001a 26
00000000004011a8 add rax, rsi
00000000004011ee mov rsi, rax
00000000004011db movzx rsi, byte ptr [rsi]
00000000004011bd xor rax, rax
00000000004011a4 add rax, rdi
00000000004011a8 add rax, rsi
00000000004011ea mov rdi, rax
00000000004011ff call _exit
;10
;25+26
00000000004011a2 pop rax
00000000004040a0
000000000040119a pop rdi
000000000000001e 30
00000000004011a4 add rax, rdi
00000000004011ea mov rdi, rax
00000000004011d6 movzx rdi, byte ptr [rdi]
00000000004011ff call _exit
;11
;30
00000000004011a2 pop rax
00000000004040a0
000000000040119a pop rdi
0000000000000009 9
00000000004011a4 add rax, rdi
00000000004011ea mov rdi, rax
00000000004011d6 movzx rdi, byte ptr [rdi]
00000000004011ff call _exit
;12
;9
00000000004011a2 pop rax
00000000004040a0
000000000040119a pop rdi
0000000000000008 8
00000000004011a4 add rax, rdi
00000000004011ea mov rdi, rax
00000000004011d6 movzx rdi, byte ptr [rdi]
00000000004011ff call _exit
;13
;8
00000000004011a2 pop rax
00000000004040a0
00000000004011ea mov rdi, rax
00000000004011d6 movzx rdi, byte ptr [rdi]
00000000004011ff call _exit
;14
;0?
00000000004011a2 pop rax
00000000004040a0
000000000040119a pop rdi
0000000000000001 1
00000000004011a4 add rax, rdi
00000000004011ea mov rdi, rax
00000000004011d6 movzx rdi, byte ptr [rdi]
00000000004011ff call _exit
;15
;1
00000000004011a2 pop rax
00000000004040a0
000000000040119a pop rdi
0000000000000002 2
00000000004011a4 add rax, rdi
00000000004011ea mov rdi, rax
00000000004011d6 movzx rdi, byte ptr [rdi]
00000000004011ff call _exit
;16
;2
00000000004011a2 pop rax
00000000004040a0
000000000040119a pop rdi
0000000000000003 3
00000000004011a4 add rax, rdi
00000000004011ea mov rdi, rax
00000000004011d6 movzx rdi, byte ptr [rdi]
00000000004011ff call _exit
;17
;3
00000000004011a2 pop rax
00000000004040a0
000000000040119a pop rdi
0000000000000004 4
00000000004011a4 add rax, rdi
00000000004011ea mov rdi, rax
00000000004011d6 movzx rdi, byte ptr [rdi]
00000000004011ff call _exit
;18
;4
00000000004011a2 pop rax
00000000004040a0
000000000040119a pop rdi
0000000000000005 5
00000000004011a4 add rax, rdi
00000000004011ea mov rdi, rax
00000000004011d6 movzx rdi, byte ptr [rdi]
00000000004011ff call _exit
;19
;5
00000000004011a2 pop rax
00000000004040a0
000000000040119a pop rdi
0000000000000006 6
00000000004011a4 add rax, rdi
00000000004011ea mov rdi, rax
00000000004011d6 movzx rdi, byte ptr [rdi]
00000000004011ff call _exit
;20
;6
00000000004011a2 pop rax
00000000004040a0
000000000040119a pop rdi
0000000000000007 7
00000000004011a4 add rax, rdi
00000000004011ea mov rdi, rax
00000000004011d6 movzx rdi, byte ptr [rdi]
00000000004011ff call _exit
;21
;7
00000000004011a2 pop rax
00000000004040a0
000000000040119a pop rdi
000000000000000b 11
00000000004011a4 add rax, rdi
00000000004011ea mov rdi, rax
00000000004011d6 movzx rdi, byte ptr [rdi]
00000000004011a2 pop rax
00000000004040a0
000000000040119c pop rsi
0000000000000000 0
00000000004011a8 add rax, rsi
00000000004011ee mov rsi, rax
00000000004011db movzx rsi, byte ptr [rsi]
00000000004011bd xor rax, rax
00000000004011a4 add rax, rdi
00000000004011a8 add rax, rsi
00000000004011ea mov rdi, rax
00000000004011ff call _exit
;22
;11+0
00000000004011a2 pop rax
00000000004040a0
000000000040119a pop rdi
000000000000001d 29
00000000004011a4 add rax, rdi
00000000004011ea mov rdi, rax
00000000004011d6 movzx rdi, byte ptr [rdi]
00000000004011ff call _exit
;23
;29
00000000004011a2 pop rax
00000000004040a0
000000000040119a pop rdi
000000000000001d 29
00000000004011a4 add rax, rdi
00000000004011ea mov rdi, rax
00000000004011d6 movzx rdi, byte ptr [rdi]
00000000004011ff call _exit
;24
;29
00000000004011a2 pop rax
00000000004040a0
000000000040119a pop rdi
000000000000001d 29
00000000004011a4 add rax, rdi
00000000004011ea mov rdi, rax
00000000004011d6 movzx rdi, byte ptr [rdi]
00000000004011a2 pop rax
00000000004040a0
000000000040119c pop rsi
000000000000000d 13
00000000004011a8 add rax, rsi
00000000004011ee mov rsi, rax
00000000004011db movzx rsi, byte ptr [rsi]
00000000004011bd xor rax, rax
00000000004011a4 add rax, rdi
00000000004011c5 sub rax, rsi
00000000004011ea mov rdi, rax
00000000004011ff call _exit
;25
;29-13
00000000004011a2 pop rax
00000000004040a0
000000000040119a pop rdi
000000000000001c 28
00000000004011a4 add rax, rdi
00000000004011ea mov rdi, rax
00000000004011d6 movzx rdi, byte ptr [rdi]
00000000004011a2 pop rax
00000000004040a0
000000000040119c pop rsi
000000000000000e 14
00000000004011a8 add rax, rsi
00000000004011ee mov rsi, rax
00000000004011db movzx rsi, byte ptr [rsi]
00000000004011bd xor rax, rax
00000000004011a4 add rax, rdi
00000000004011c5 sub rax, rsi
00000000004011ea mov rdi, rax
00000000004011ff call _exit
;26
;28-14
00000000004011a2 pop rax
00000000004040a0
000000000040119a pop rdi
000000000000001c 28
00000000004011a4 add rax, rdi
00000000004011ea mov rdi, rax
00000000004011d6 movzx rdi, byte ptr [rdi]
00000000004011a2 pop rax
00000000004040a0
000000000040119c pop rsi
000000000000000f 15
00000000004011a8 add rax, rsi
00000000004011ee mov rsi, rax
00000000004011db movzx rsi, byte ptr [rsi]
00000000004011bd xor rax, rax
00000000004011a4 add rax, rdi
00000000004011a8 add rax, rsi
00000000004011ea mov rdi, rax
00000000004011ff call _exit
;27
;28+15
00000000004011a2 pop rax
00000000004040a0
000000000040119a pop rdi
0000000000000000 0
00000000004011a4 add rax, rdi
00000000004011ea mov rdi, rax
00000000004011d6 movzx rdi, byte ptr [rdi]
00000000004011a2 pop rax
00000000004040a0
000000000040119c pop rsi
000000000000001b 27
00000000004011a8 add rax, rsi
00000000004011ee mov rsi, rax
00000000004011db movzx rsi, byte ptr [rsi]
00000000004011bd xor rax, rax
00000000004011a4 add rax, rdi
00000000004011c5 sub rax, rsi
00000000004011ea mov rdi, rax
00000000004011ff call _exit
;28
;0-27
00000000004011a2 pop rax
00000000004040a0
000000000040119a pop rdi
0000000000000017 23
00000000004011a4 add rax, rdi
00000000004011ea mov rdi, rax
00000000004011d6 movzx rdi, byte ptr [rdi]
00000000004011a2 pop rax
00000000004040a0
000000000040119c pop rsi
0000000000000018 24
00000000004011a8 add rax, rsi
00000000004011ee mov rsi, rax
00000000004011db movzx rsi, byte ptr [rsi]
00000000004011bd xor rax, rax
00000000004011a4 add rax, rdi
00000000004011c5 sub rax, rsi
00000000004011ea mov rdi, rax
00000000004011ff call _exit
;29
;23-24
00000000004011a2 pop rax
00000000004040a0
000000000040119a pop rdi
000000000000001a 26
00000000004011a4 add rax, rdi
00000000004011ea mov rdi, rax
00000000004011d6 movzx rdi, byte ptr [rdi]
00000000004011a2 pop rax
00000000004040a0
000000000040119c pop rsi
0000000000000000 0
00000000004011a8 add rax, rsi
00000000004011ee mov rsi, rax
00000000004011db movzx rsi, byte ptr [rsi]
00000000004011a2 pop rax
00000000004040a0
000000000040119e pop rdx
0000000000000001 1
00000000004011ac add rax, rdx
00000000004011f2 mov rdx, rax
00000000004011e0 movzx rdx, byte ptr [rdx]
00000000004011bd xor rax, rax
00000000004011a4 add rax, rdi
00000000004011a8 add rax, rsi
00000000004011c9 sub rax, rdx
00000000004011ea mov rdi, rax
00000000004011ff call _exit
;30
;26+0-1
00000000004011a2 pop rax
00000000004040a0
000000000040119a pop rdi
0000000000000013 19
00000000004011a4 add rax, rdi
00000000004011ea mov rdi, rax
00000000004011d6 movzx rdi, byte ptr [rdi]
00000000004011ff call _exit
;31
;19
00000000004011a2 pop rax
00000000004040a0
000000000040119a pop rdi
000000000000000b 11
00000000004011a4 add rax, rdi
00000000004011ea mov rdi, rax
00000000004011d6 movzx rdi, byte ptr [rdi]
00000000004011a2 pop rax
00000000004040a0
000000000040119c pop rsi
000000000000000c 12
00000000004011a8 add rax, rsi
00000000004011ee mov rsi, rax
00000000004011db movzx rsi, byte ptr [rsi]
00000000004011bd xor rax, rax
00000000004011a4 add rax, rdi
00000000004011a8 add rax, rsi
00000000004011ea mov rdi, rax
00000000004011ff call _exit
;32
;11+12
00000000004011a2 pop rax
00000000004040a0
000000000040119a pop rdi
0000000000000015 21
00000000004011a4 add rax, rdi
00000000004011ea mov rdi, rax
00000000004011d6 movzx rdi, byte ptr [rdi]
00000000004011a2 pop rax
00000000004040a0
000000000040119c pop rsi
0000000000000014 20
00000000004011a8 add rax, rsi
00000000004011ee mov rsi, rax
00000000004011db movzx rsi, byte ptr [rsi]
00000000004011bd xor rax, rax
00000000004011a4 add rax, rdi
00000000004011c5 sub rax, rsi
00000000004011ea mov rdi, rax
00000000004011ff call _exit
;33
;21-200x4040a0是main程序中存放读入的flag的
z3解方程组
通过上面的汇编,可以看出就是flag的字符之间加加减减满足一定的等式,很明显可以用z3暴力求解:
from z3 import *
s = Solver()
f = []
for i in range(31):
f.append(BitVec('f_'+str(i), 8))
r = [208, 225, 237, 20, 214, 183, 79, 105, 207, 217, 125, 66, 123, 104, 97, 99, 107 , 105, 109, 50, 48, 202, 111, 111, 29, 63, 223, 36, 0, 124, 100, 219, 32]
s.add(f[0]+f[2]+f[4]-100 == r[0])
s.add(f[6]+f[8]+f[10] == r[1])
s.add(f[12]+f[14]+f[16] == r[2])
s.add(f[18]+f[1]-f[30] == r[3])
s.add(f[3]+f[22]+f[3]-100 == r[4])
s.add(f[5]+f[29]+f[28]-f[7]-100 == r[5])
s.add(f[9]+f[17]-f[11] == r[6])
s.add(f[13]+f[15]+f[20]-f[19]-f[27] == r[7])
s.add(f[21]+f[23]+f[23] == r[8])
s.add(f[25]+f[26] == r[9])
s.add(f[30] == r[10])
s.add(f[9] == r[11])
s.add(f[8] == r[12])
s.add(f[0] == r[13])
s.add(f[1] == r[14])
s.add(f[2] == r[15])
s.add(f[3] == r[16])
s.add(f[4] == r[17])
s.add(f[5] == r[18])
s.add(f[6] == r[19])
s.add(f[7] == r[20])
s.add(f[11]+f[0] == r[21])
s.add(f[29] == r[22])
s.add(f[29] == r[23])
s.add(f[29]-f[13] == r[24])
s.add(f[28]-f[14] == r[25])
s.add(f[28]+f[15] == r[26])
s.add(f[0]-f[27] == r[27])
s.add(f[23]-f[24] == r[28])
s.add(f[26]+f[0]-f[1] == r[29])
s.add(f[19] == r[30])
s.add(f[11]+f[12] == r[31])
s.add(f[21]-f[20] == r[32])
print(s.check())
n = []
for i,name in enumerate(f):
n.append(s.model()[name].as_long())
print(''.join(list(map(chr,n))))由于只有33个等式,正则提取又比较麻烦,所有我直接手动输入的等式关系。
注意33个等式,不代表flag有33个字符!!
举个最简单的例子,a+b=2,a+b+c=3,a+b-c=1,a+c=2四个等式三个变量。
变量的个数要从汇编代码中找.
坑了我一整天的地方
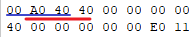
一开始我提取并没有提取payload中前缀字符串a之后的全部8字节一组的数据,而是提取了payload中地址,脚本找不到了,反正算法就是找到0x40的字符的位置i,然后提取date[i-2,i](因为所有的地址都是40xxxx,小端序就是0x40在最后面),提取出的前几行地址:
4011a2
40a000
4040a0
40119a
4011a4
4011ea
4011d6
4011a2
40a000
4040a0
40119c
4011a8
4011ee
4011db生成的汇编为:
4011a2 pop rax ;1
40a000
4040a0
40119a pop rdi
4011a4 add rax, rdi
4011ea mov rdi, rax
4011d6 movzx rdi, byte ptr [rdi] ;rdi += rax
4011a2 pop rax ;2
40a000
4040a0
40119c pop rsi
4011a8 add rax, rsi
4011ee mov rsi, rax
4011db movzx rsi, byte ptr [rsi] ;rsi += rax0x4040a0是flag的地址,但是main程序中没有0x40a000这个地址。
最后才发现我的算法遇到0x4040a0时,因为有两个0x40,所以会提取两次,一次是40a000,第二次是0x4040a0.
其次,我还犯了一个致命的错误,payload中不只是地址,还有一些数据,不然只有pop指令,没有数据,不可能实现。
我就是因为生成的汇编代码中一堆pop,而没有任何一个数字,而看不懂汇编的。
当采用删去前缀字符串a,八字节一组,小端转大端的算法提取汇编后,payload实现的功能就很容易看懂了,只有加法和减法而已。
大佬的题解
今天看到了一个大佬的题解,全自动脚本,他是直接把用的的汇编指令模拟了一遍。
从他的脚本中我学到了一些新知识:
- 善用pwn的u64,从而不需要自己转换大小端序
- 使用pwn的log.info输出flag,使得输出简介好看。
我给脚本添加了一些关键的注释。
#!/usr/bin/python2
import pwn
import z3
class ROP(object):
def __init__(self, payload, stack_size=7):
self.payload = payload
for i in range(stack_size):
self.pop()
def pop(self):
data = pwn.u64(self.payload[:8])
self.payload = self.payload[8:]
return data
def rop(self):
while len(self.payload) != 0:
ret_addr = self.pop()
if ret_addr == 0x40119A:
self.rdi = self.pop()
elif ret_addr == 0x40119C:
self.rsi = self.pop()
elif ret_addr == 0x40119E:
self.rdx = self.pop()
elif ret_addr == 0x4011A0:
self.rcx = self.pop()
elif ret_addr == 0x4011A2:
self.rax = self.pop()
elif ret_addr == 0x4011A4:
self.rax += self.rdi
elif ret_addr == 0x4011A8:
self.rax += self.rsi
elif ret_addr == 0x4011AC:
self.rax += self.rdx
elif ret_addr == 0x4011B0:
self.rax += self.rcx
elif ret_addr == 0x4011B4:
self.rax += self.rax
elif ret_addr == 0x4011B8:
self.rax += 1
elif ret_addr == 0x4011BD:
self.rax ^= self.rax
elif ret_addr == 0x4011C1:
self.rax -= self.rdi
elif ret_addr == 0x4011C5:
self.rax -= self.rsi
elif ret_addr == 0x4011C9:
self.rax -= self.rdx
elif ret_addr == 0x4011CD:
self.rax -= self.rcx
elif ret_addr == 0x4011D1:
self.rax -= 1
#movzx rdi, byte ptr [rdi]
elif ret_addr == 0x4011D6:
assert 0x4040A0 <= self.rdi < 0x4040A0 + 0x1F
self.rdi = flag[self.rdi - 0x4040A0]
elif ret_addr == 0x4011DB:
assert 0x4040A0 <= self.rsi < 0x4040A0 + 0x1F
self.rsi = flag[self.rsi - 0x4040A0]
elif ret_addr == 0x4011E0:
assert 0x4040A0 <= self.rdx < 0x4040A0 + 0x1F
self.rdx = flag[self.rdx - 0x4040A0]
elif ret_addr == 0x4011E5:
assert 0x4040A0 <= self.rcx < 0x4040A0 + 0x1F
self.rcx = flag[self.rcx - 0x4040A0]
elif ret_addr == 0x4011EA:
self.rdi = self.rax
elif ret_addr == 0x4011EE:
self.rsi = self.rax
elif ret_addr == 0x4011F2:
self.rdx = self.rax
elif ret_addr == 0x4011F6:
self.rcx = self.rax
elif ret_addr == 0x4011FF:
return self.rdi
# z3变量组成的列表
flag = [z3.Int('flag[{}]'.format(i)) for i in range(0x1F)]
o = [296, 272, 272, 272, 296, 360, 272, 424, 272, 208, 120, 120, 120, 96, 120, 120, 120, 120, 120, 120, 120, 208, 120, 120, 208, 208, 208, 208, 208, 272, 120, 208, 208]
r = [208, 225, 237, 20, 214, 183, 79, 105, 207, 217, 125, 66, 123, 104, 97, 99, 107 , 105, 109, 50, 48, 202, 111, 111, 29, 63, 223, 36, 0, 124, 100, 219, 32]
rets = []
with open('blob', 'rb') as f:
for offset in o:
data = f.read(offset)
rets.append(ROP(data).rop())
s = z3.Solver()
for i in range(len(r)):
s.add(rets[i] == r[i])
pwn.log.info(s.check())
m = s.model()
flag_str = ''
for ch in flag:
flag_str += chr(m[ch].as_long())
pwn.log.info(flag_str)注意本脚本是python3的,依赖pwn和z3-solver,可由下面的语句安装。
pip3 install --upgrade git+https://github.com/arthaud/python3-pwntools.git
pip3 install z3-solver对于flag这个列表可能有些疑问,其实他是一个z3变量组成的列表,输出flag这个列表可以看到:
[flag[0], flag[1], flag[2], flag[3], flag[4], flag[5], flag[6], flag[7], flag[8], flag[9], flag[10], flag[11], flag[12], flag[13], flag[14], flag[15], flag[16], flag[17], flag[18], flag[19], flag[20], flag[21], flag[22], flag[23], flag[24], flag[25], flag[26], flag[27], flag[28], flag[29], flag[30]]